Security workflow automation for everyone
Explore modern ways of penetration testing and vulnerability management
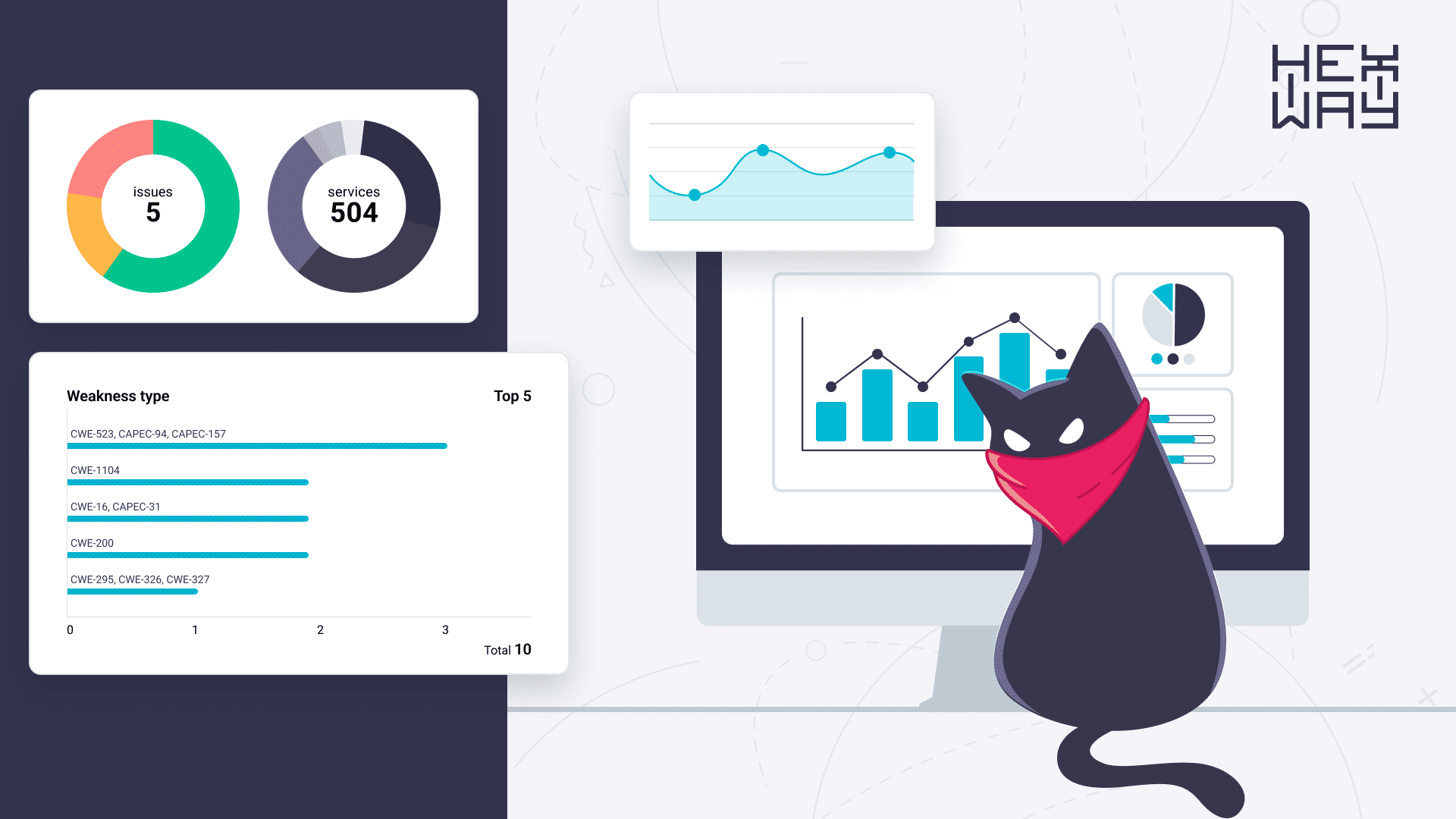
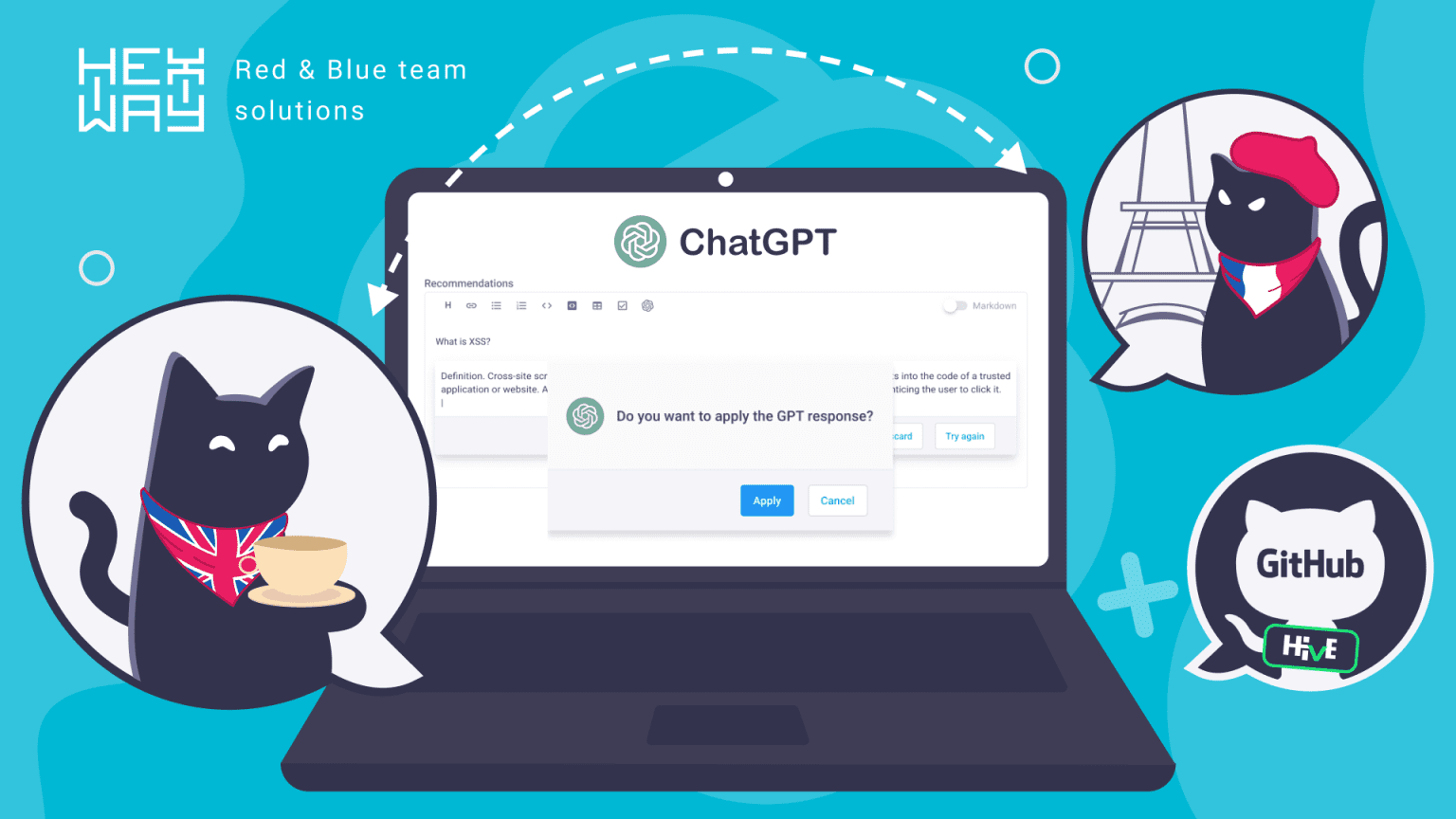
Optimize your workflow
Automate
Reduce routine at each stage of your pentest by optimizing the workflow

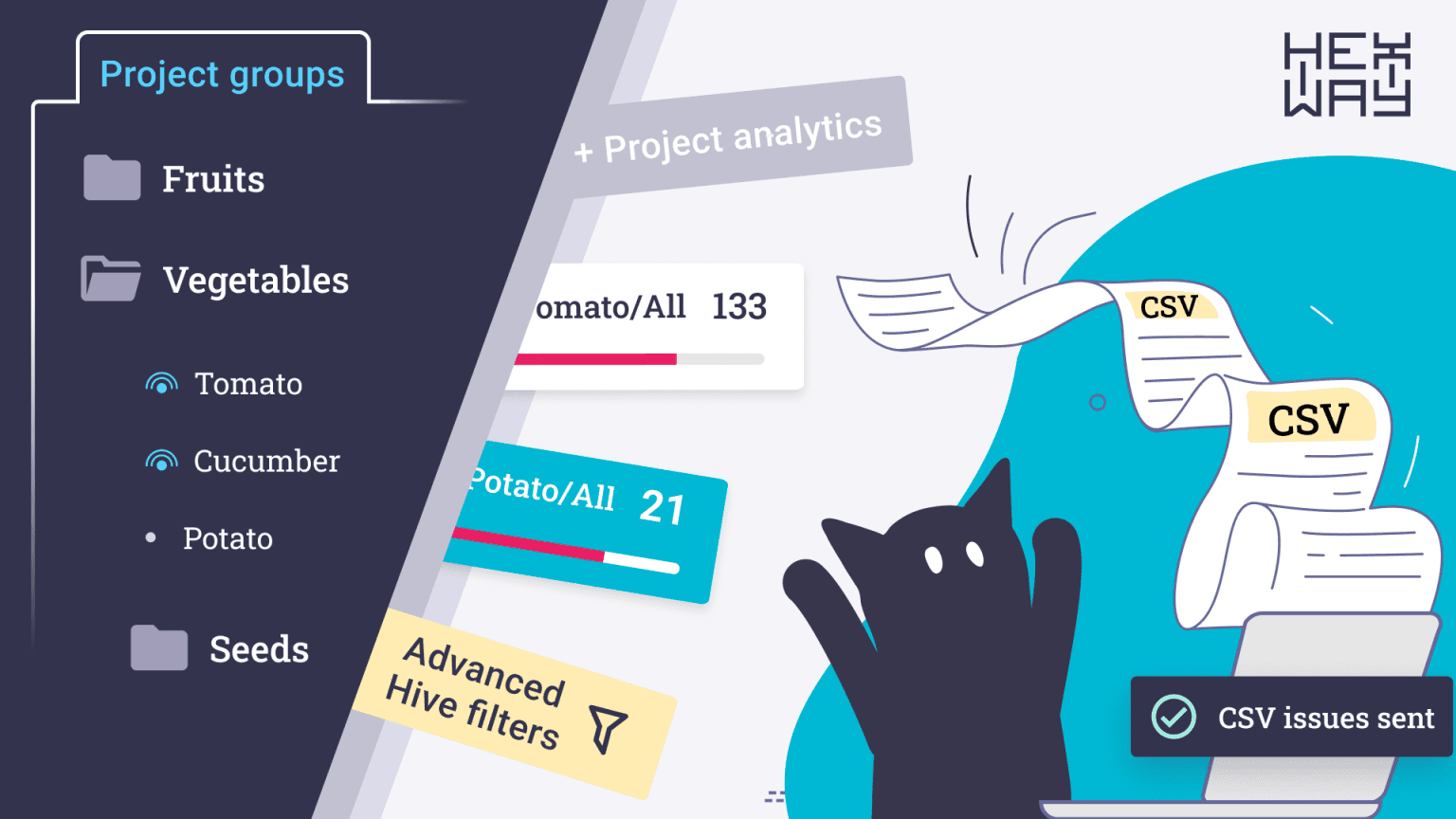
Aggregate
Work with your security tool outputs in one place

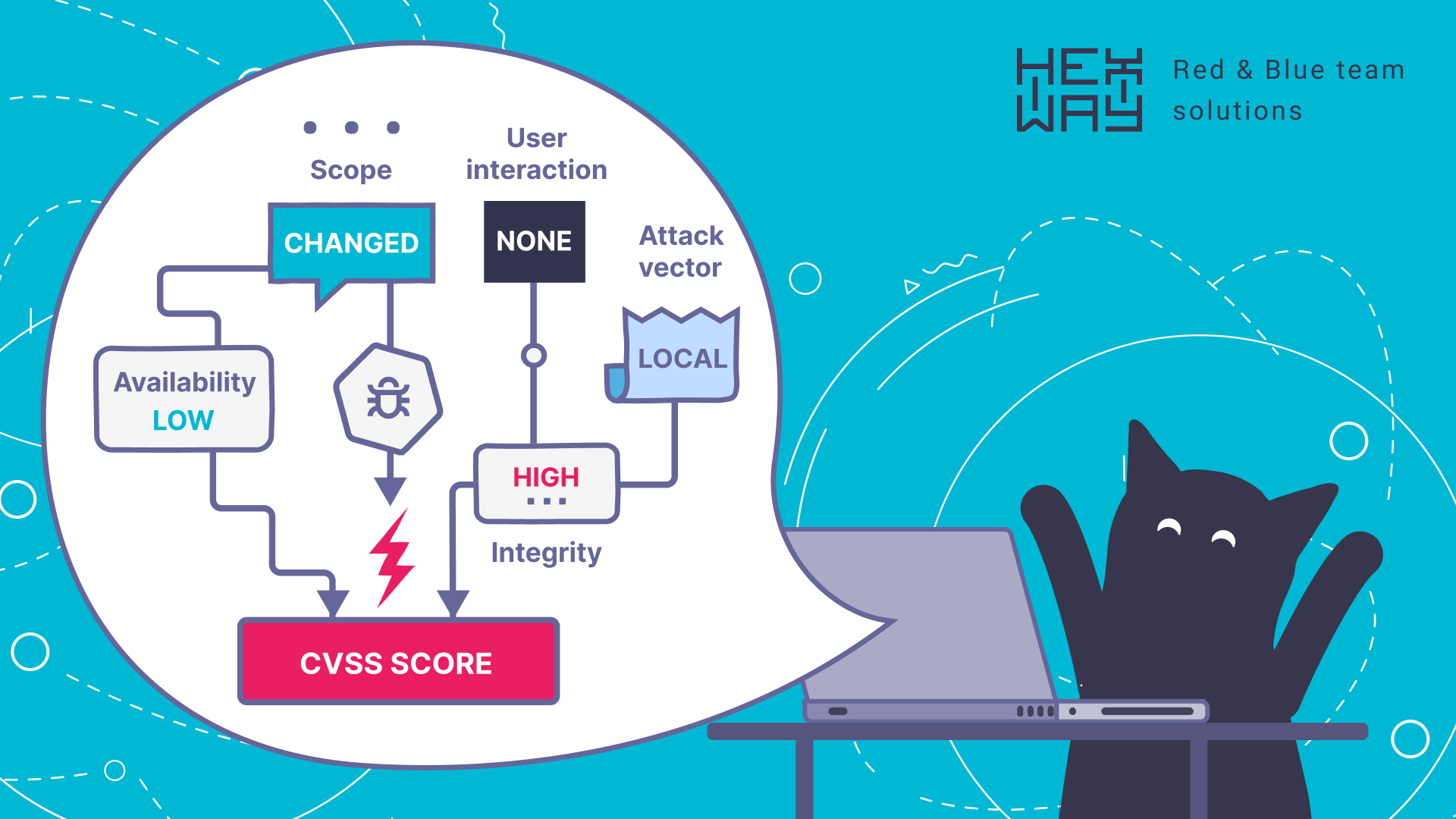
Prioritize
Set goals and tasks for the team based on severity score

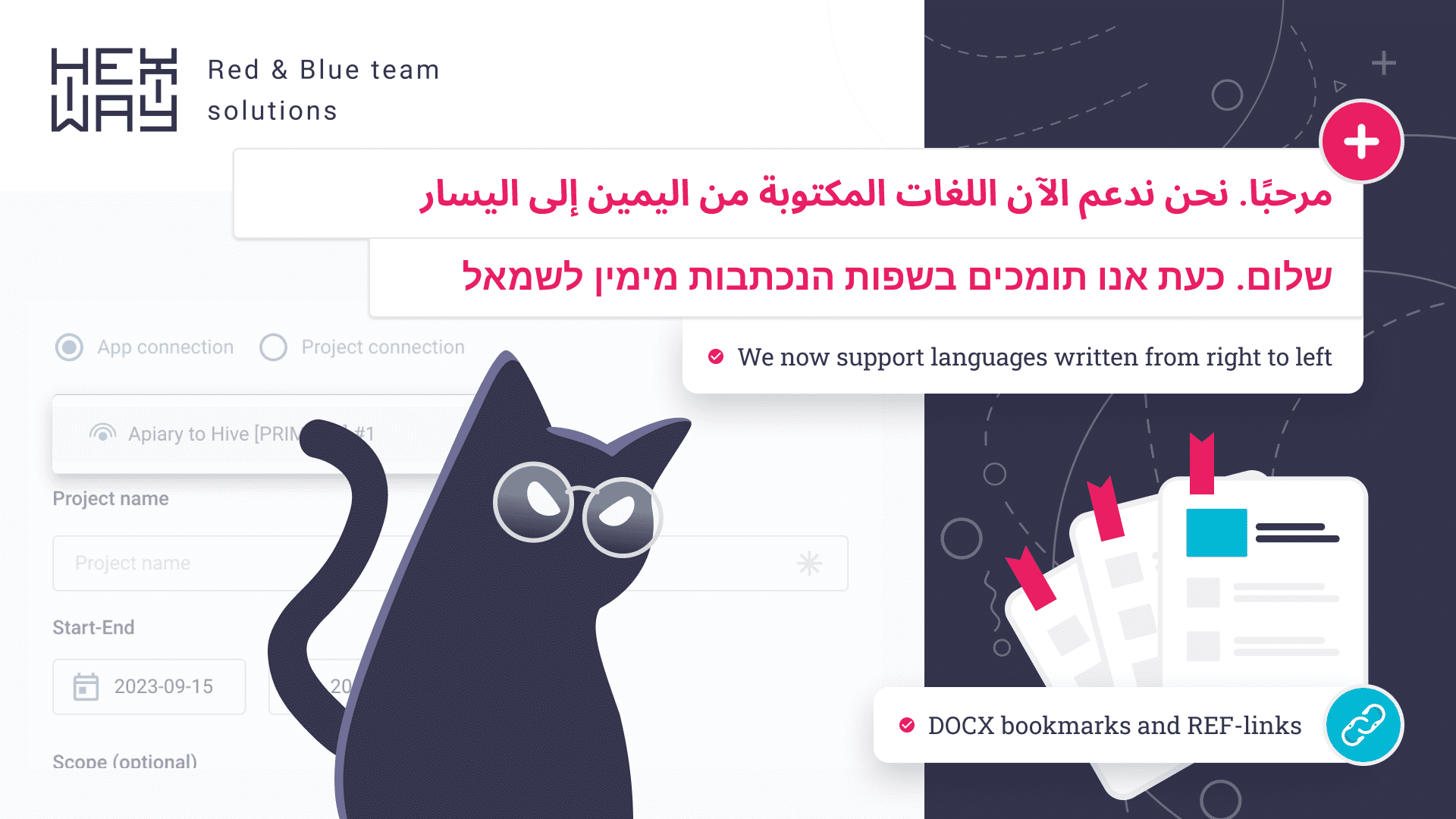
Share
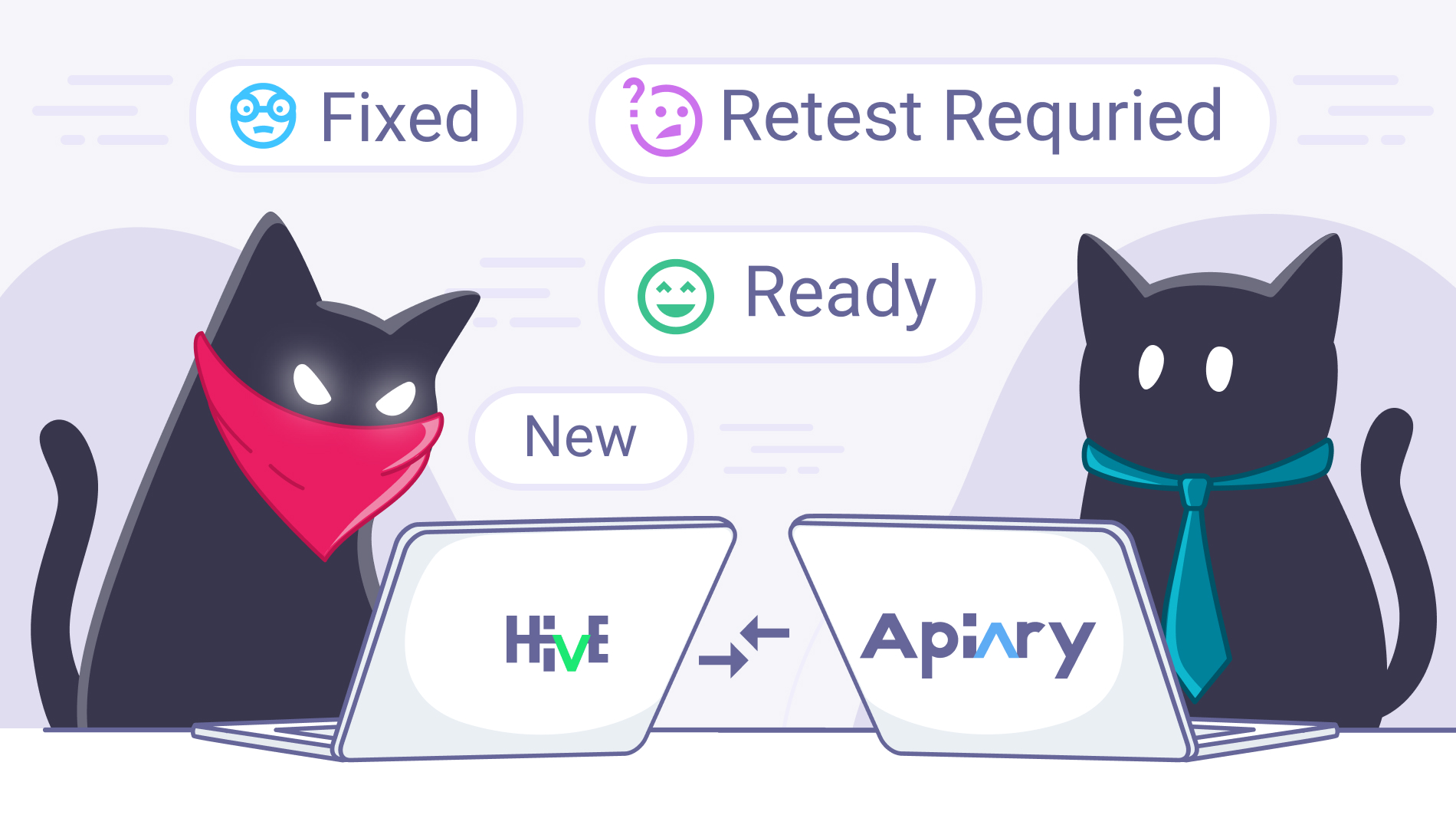
Deliver pentest results in real-time via customizable customer portal

Pick what your security posture needs
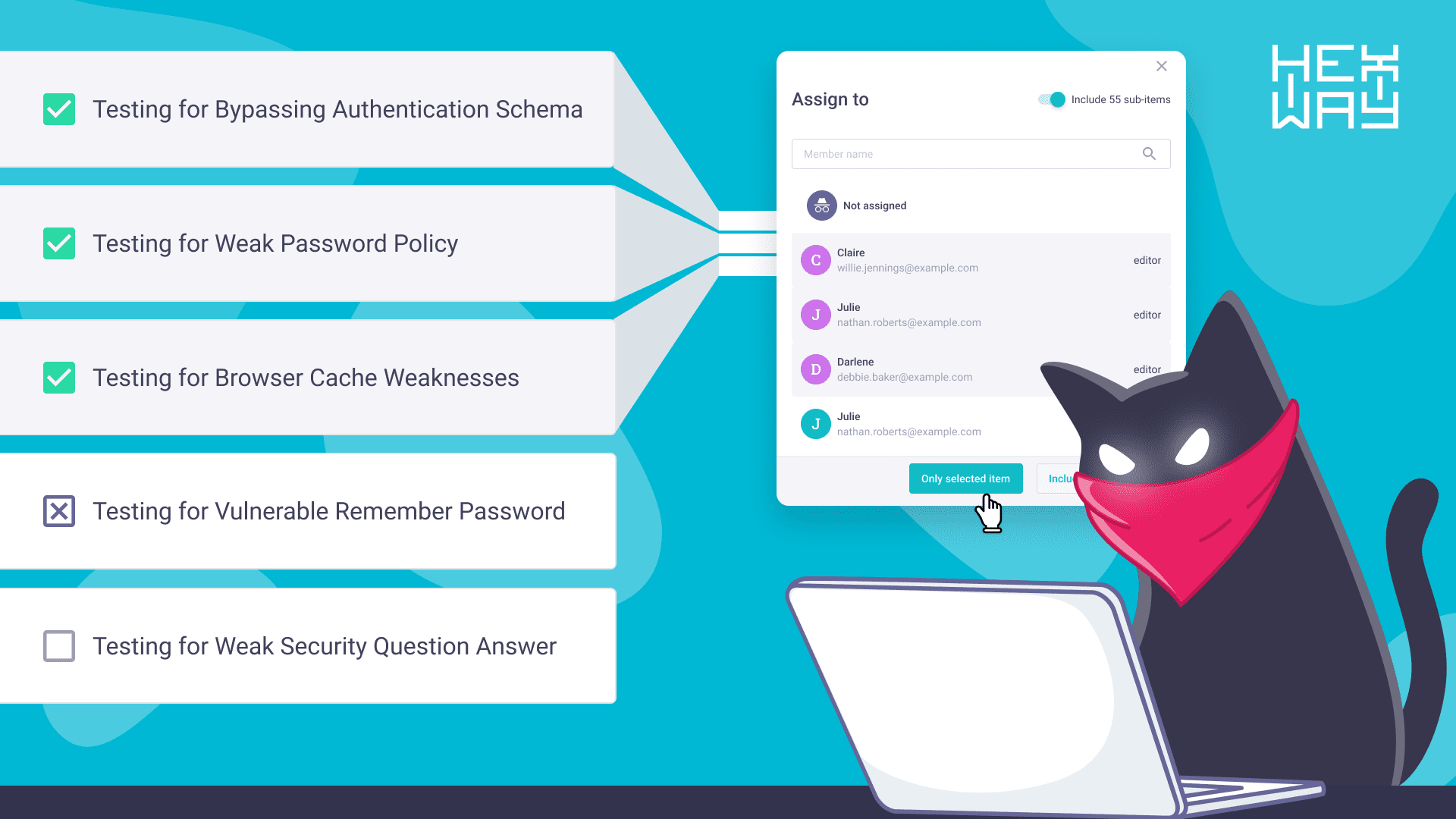
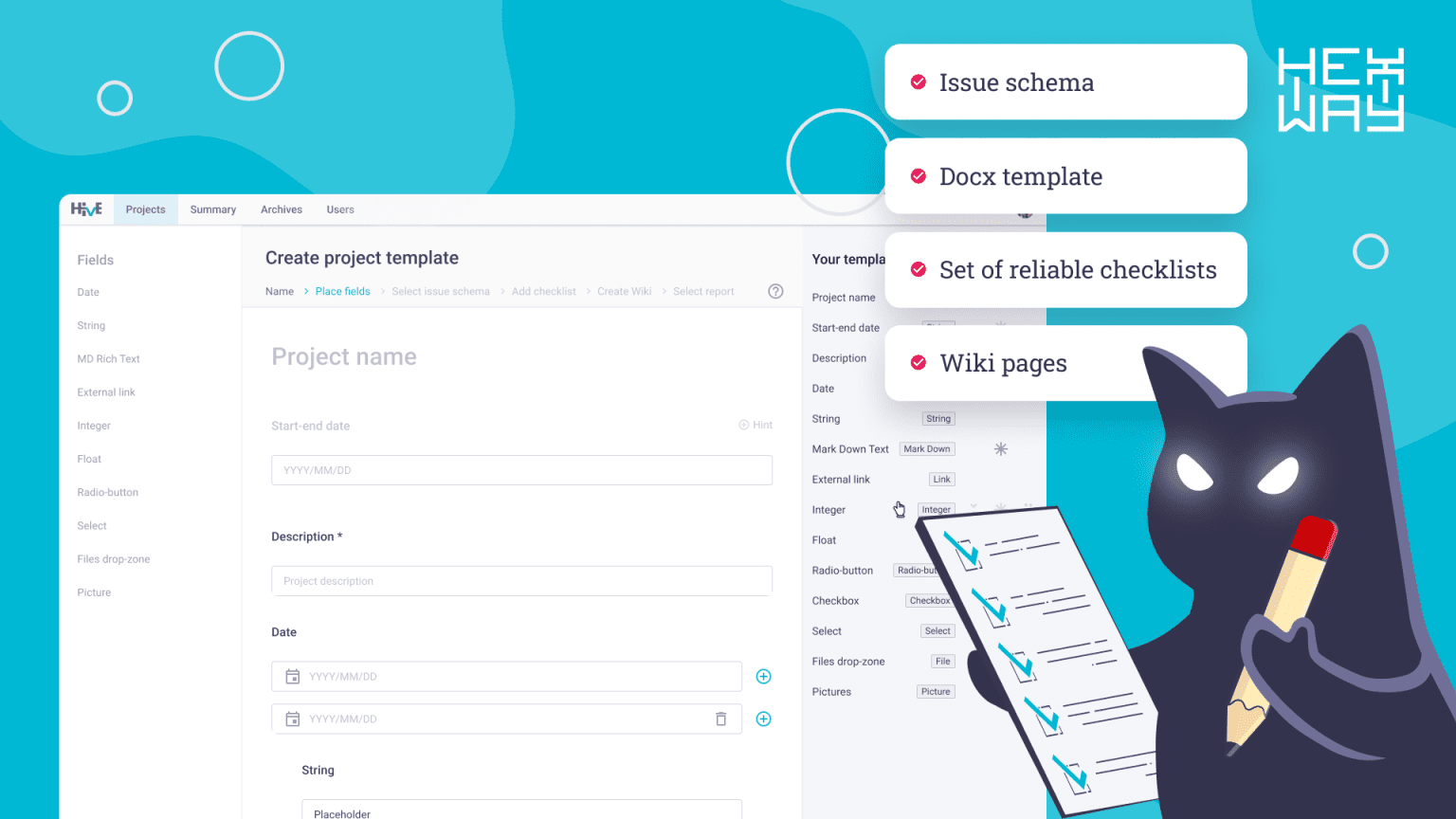
Reduce pentest routine
Pentest automation tool to optimise each step of security workflow.
Unite customers and pentesters in one environment to provide awesome pentests and save time on routine tasks.
Learn more
Free-foreverversion available





Unify application security
ASOC solution to aggregate security issues from different security scanners in one place.
Work with security tools output fast, convenient and productive.
Learn more
Over 10 000 findingsprocessed every week
What fits your profile?

CISO/CTO
- Dashboards
- Top-tier reports
- Pentest project planner
- Checklists & methodologies
- Faster remediation

AppSec
- Remediation control
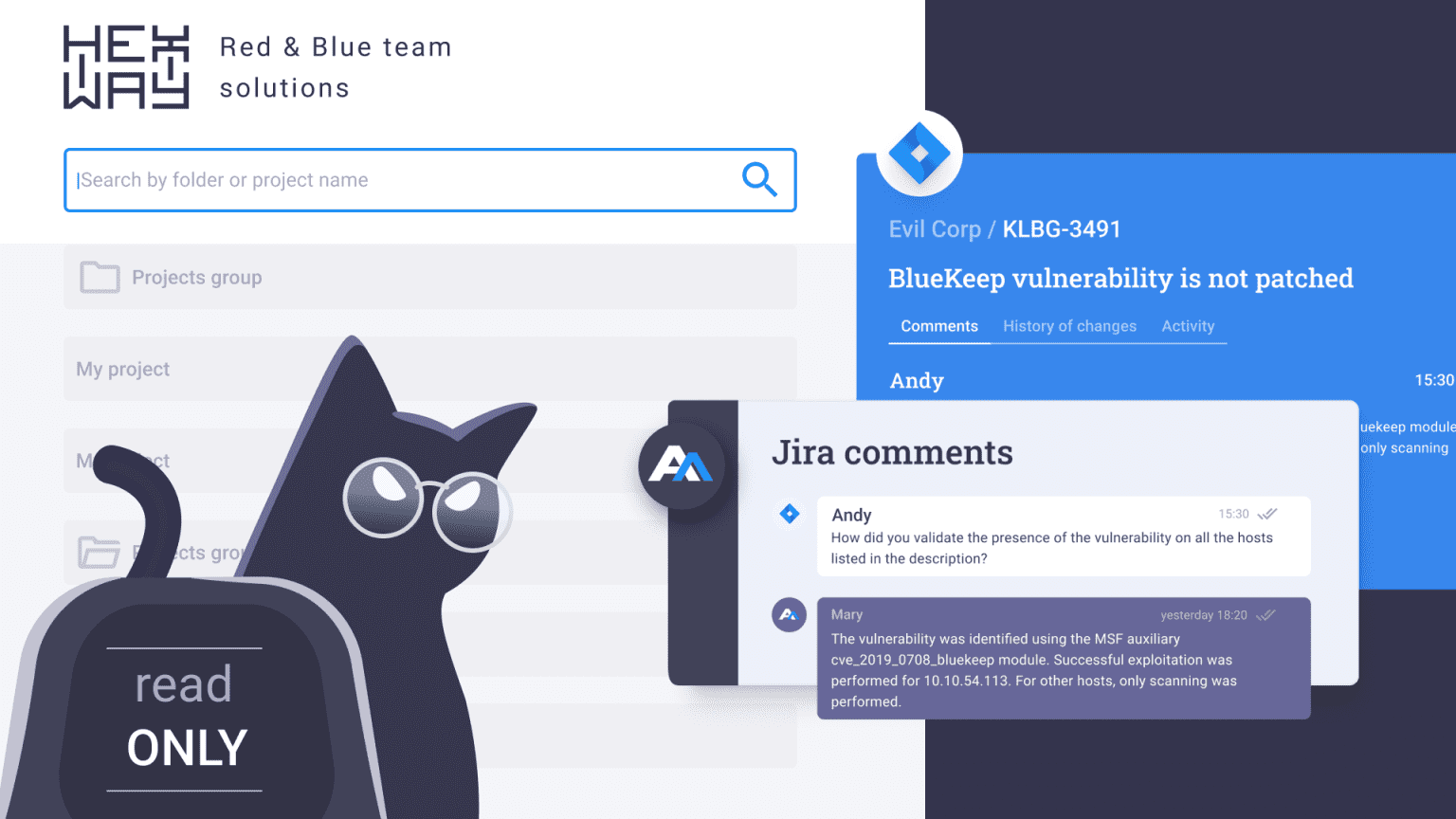
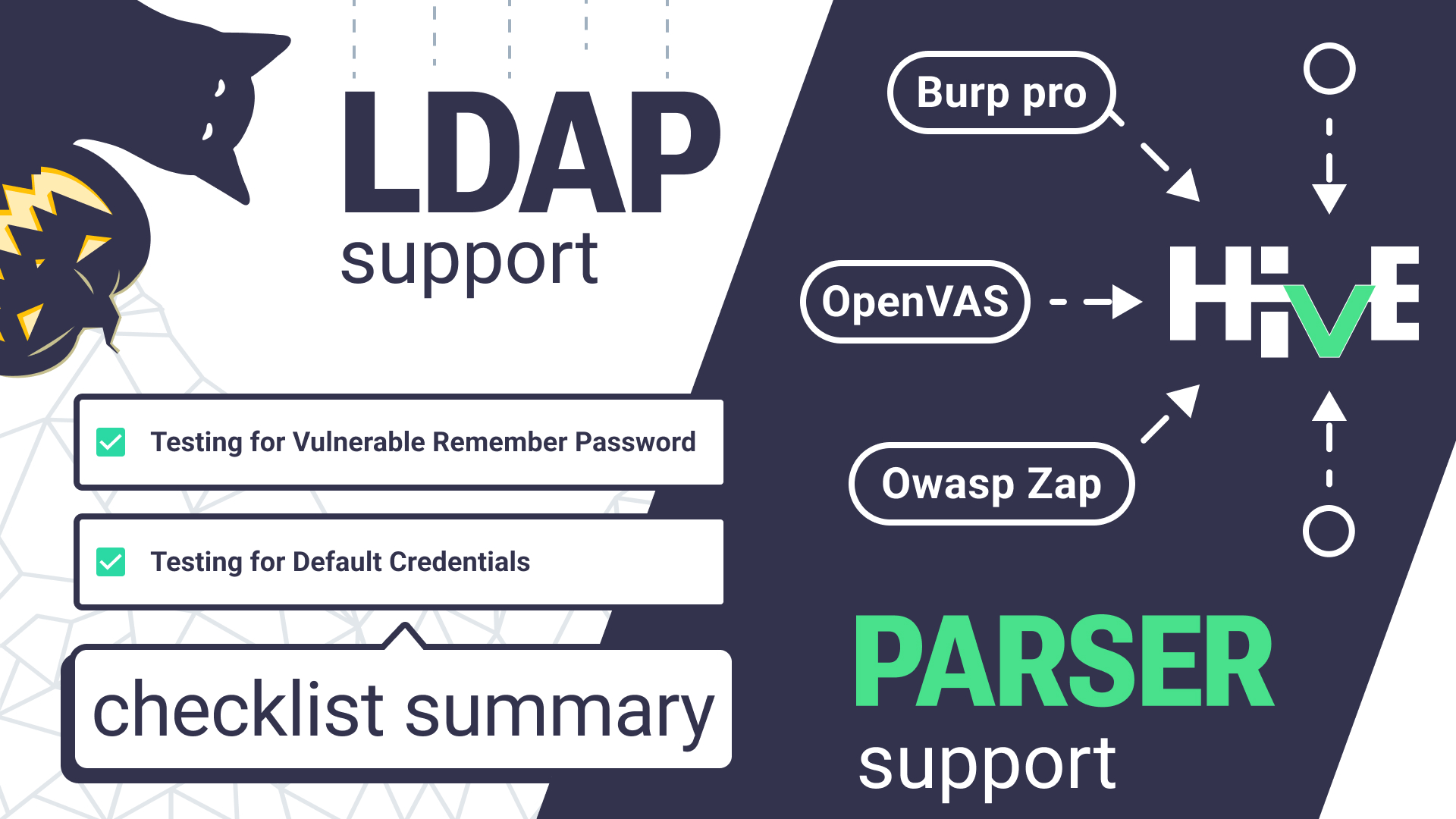
- Tool integrations
- Bug-as-a-ticket
- Continuous monitoring
- Issue stats
Reviews
Cristian Morillas Diaz
ESET Latam
Hexway is a fast, effective platform, with a responsive design that facilitates the daily work of the pentester. Our clients had a good reception of Apiary, and the fully customizable reports.The Hexway team adds features frequently and has a quick response when there are problems.
Nicolas Krassas
from Henkel
Since a lot of critical issues could be found when performing penetration testing, the platform allows to address them immediately, thus reducing the remediation time in such critical cases. The more we learn, study, and focus on the latest features, the better we can take advantage of the capabilities and enhance our workflow.
Chris Abou-Chabké
from BlackHat Ethical Hacking
A very nice work, very responsive interface even with large amount of data. Import works without an issue from different sources. Very nice work overall and fast UI. I'm able to share with fellow testers results and import from my tools. Hope to see more features coming soon!
Xtreme Pentesting
Traw
By far the best pentest platform I've found, not only in terms of quality and responsiveness of the user interface but also in terms of making it easier to discover and report vulnerabilities in websites and network infrastructures. I can import data from my favorite tools and share the results with other pentesters thanks to the integration capability. More integrations imply easier pentesting!

How does Hive save up to 6 hours on each pentest project?
Stay up to date
Greate!
Check your mail